In the first part of this 2 part article I discussed several science fiction style conspiracy theories surrounding the internet, and mega corporations using it's power for nefarious agendas. While I mentioned the "Matrix" and "The Truman Show" admittedly the majority of the article was focused around my own personal project that if I ever were to write a science fiction novel it would look similar to that. The idea that through the use of the internet "reality" is slowly being infiltrated, and altered. Quietly, little by little, day by day, the reality of the world around us, what we come to believe is reality, is becoming more fabricated, and more false.
While I believe this would make for a great book unfortunately I think what is really happening is less thrilling, and more insulting towards the human race.
I truly think all the world is a stage, and there are various plays of different sizes going on, many simultaneously, involving actors of different caliber. I believe that there are often unseen forces manipulating the way the world works, to discuss their reasons is to lessen the discussion on their existence.
I believe that those who pull the strings knew of "the internet" at least how we currently know it today. Surely they knew the some of the consequences, and ultimately after it's inception those with less foresight, but great intellect devised ideas such as an "internet of things" in which our everyday household items are spying on us. Where the next war might not be fought on a battle field with guns, but rather a cyber war with hackers going back and forth, using slow methodical logic, and a propaganda war likely waged on a countries own citizens. However, I believe the internet, and it's powers came about much faster than anticipated.
Read more...
Showing posts with label cyber security. Show all posts
Showing posts with label cyber security. Show all posts
Wednesday, May 21, 2014
Is the Power of the Internet Being Purposely Withheld? Part 1
[Authors Note: This is a very long article that covers a wide range of things, I could have separated them up into smaller articles, however, I had planned on writing an article about the limitation of the internet, and this is how it ended. I feel there is a good deal of information in this article.]
Great minds over the years have written numerous science fiction books that were decades head of the time, and over those years time, and time again we have seen science fiction because science fact. It would seem that the limitation of humans lies nested in the ability to create a thought. If it can be thought, it can be done, albeit eventually.
Look at Walt Disney's "Carousel of Progress", which is a focal point of one of my upcoming articles, for a good example of how much the only only limit is the thought. "If you can dream it, you can do it" - Which was said by none other than Walt Disney. Throughout the Carousel of Progress ride there are numerous things that were predicted, or laughed at the possibility of, as seen from a time previous in the time line. For example the main character, and narrator of the Carousel of Progress, states at one point that he's "even heard of two fellas who are working on some sort of flying machine....ahh it will never work". Of course the wright brothers did in fact get their plane flying, in in less than a century man went from having horse drawn carriages to nuclear powered aircraft carries.
That all being said, we come to the internet. I don't think that the "powers that be" had any idea of just how fast the internet would change the world. Maybe it's changing things just a little too fast for some of their own liking.
There are many theories about the internet, and the unseen hand pulling the strings of reality. For example there is the possibility that a service such as Google could actually be showing you what it thinks you want to see, and if done to a well enough extent, no one would ever know. A sort of mix between the "Truman Show" and "The Matrix".
Read more...
Great minds over the years have written numerous science fiction books that were decades head of the time, and over those years time, and time again we have seen science fiction because science fact. It would seem that the limitation of humans lies nested in the ability to create a thought. If it can be thought, it can be done, albeit eventually.
Look at Walt Disney's "Carousel of Progress", which is a focal point of one of my upcoming articles, for a good example of how much the only only limit is the thought. "If you can dream it, you can do it" - Which was said by none other than Walt Disney. Throughout the Carousel of Progress ride there are numerous things that were predicted, or laughed at the possibility of, as seen from a time previous in the time line. For example the main character, and narrator of the Carousel of Progress, states at one point that he's "even heard of two fellas who are working on some sort of flying machine....ahh it will never work". Of course the wright brothers did in fact get their plane flying, in in less than a century man went from having horse drawn carriages to nuclear powered aircraft carries.
That all being said, we come to the internet. I don't think that the "powers that be" had any idea of just how fast the internet would change the world. Maybe it's changing things just a little too fast for some of their own liking.
There are many theories about the internet, and the unseen hand pulling the strings of reality. For example there is the possibility that a service such as Google could actually be showing you what it thinks you want to see, and if done to a well enough extent, no one would ever know. A sort of mix between the "Truman Show" and "The Matrix".
Read more...
Monday, April 21, 2014
Be Mindful of Privacy & Security with Shortened URLS- Goo.gl Known Security Flaw Benefits Those who Know How to Use It
Most people have become accustomed to shortened URL's. The purpose is to take some long link, and make it much smaller in the number of characters. More devious usages of shortened URL's is to change a link to a porn website to something like www.bla.gl/sje so the viewer right away doesn't know where the link they are clicking is going to go.
In the second scenario mentioned this has been a concern for some time, and there is an easy fix http://www.longurl.ORG (*See asterisk below for important longurl info) This website will allow you to enter any shortened URL, and show you where it leads to. Protecting you from accidentally clicking on a shortened URL that you wouldn't have clicked in the previous days of hovering ones mouse over the link to show where it leads.
 |
| "OLD" Style of checking destination of a link - |
Read more...
Labels:
cyber security,
Google,
NSA,
Prison Internet,
secrecy,
Technology,
Tracking
Thursday, March 20, 2014
"Cyber-Hijacking" of Flight #370 - State Sponsored Terrorism
A series of articles published in The International Business Times and Israel Defense has been floating the idea of the missing Malaysia Airlines being "cyber-hijacked". According to several security experts a Boeing-777 airplane can have codes inserted into it using a cell phone, or a USB stick.
There are some issues, and concerns that are raised if a cyber-hijacking is to be taken as a legitimate possibility.
The type of cyber-attacks mentioned in the article would not be able to remotely fly the airplane, make precise turns, altitude changes, etc. The type of attack involves inserting codes that would likely result in the crash of the airplane either due to mechanical failures, or causing human error. There has been no evidence that the plane has crashed, nor was there any ransom made threatening to crash the plane via exploit.
One major issue not covered about a cyber-hijacking has to do with the involvement of the pilot. If the pilot was not involved in the plot then the hijackers would have to neutralize the pilot in some fashion. Otherwise not only would the pilot be able to override the autopilot, and attempt to thwart the hijacking, but would also be able to radio that something was wrong. Since there was no mayday messages from the pilot it leads to the possibility that the pilot was involved.
It seems highly unlikely that the pilot would have the technical programming abilities to write a sophisticated set of code that would be involved in a cyber-hijacking. This means that a cyber-hijacking would have to be a team effort. The pilot for his abilities with flying the aircraft, knowledge of the air corridors, and unrestricted access to the cock-pit for manual maneuvers such as turning off the transponder. If the effects of a cyber attack on the plane was disabling certain programs, beacons, etc that the pilot would not normally be able to alter and was carried out via a cell phone there would be no need for additional team members to physically board the plane. The pilot could carry the phone, and activate the code insertion himself, or another member could physically board the plane who may or may not be the person who wrote the code. Regardless of the number of members on board the plane a cyber-hijacking of the plane would require a minimum of two members, the pilot and the code-writer.
It is highly unlikely that the typical image of a "terrorist" that the Western media portrays, i.e. a turban wearing, camel riding, middle-Eastern man in a cave, would either have the knowledge of how a Boeing-777 computer works in order to program code that was effective, or would be in the market for someone to write such code without gaining international attention. On the other hand the United States or Israel could easily gain the knowledge of exactly how the systems work as well as have numerous people already on the payroll with the ability to write such codes.
If a cyber-hijacking occurred in connection with missing Malaysian flight #370 it was not a lone wolf, a rogue pilot, or an Al-Cia-da terrorist. It would have been a highly sophisticated operation that would require the vast resources of a state to carry out. However the Western media will have you believe the exact opposite.
Read more...
There are some issues, and concerns that are raised if a cyber-hijacking is to be taken as a legitimate possibility.
The type of cyber-attacks mentioned in the article would not be able to remotely fly the airplane, make precise turns, altitude changes, etc. The type of attack involves inserting codes that would likely result in the crash of the airplane either due to mechanical failures, or causing human error. There has been no evidence that the plane has crashed, nor was there any ransom made threatening to crash the plane via exploit.
One major issue not covered about a cyber-hijacking has to do with the involvement of the pilot. If the pilot was not involved in the plot then the hijackers would have to neutralize the pilot in some fashion. Otherwise not only would the pilot be able to override the autopilot, and attempt to thwart the hijacking, but would also be able to radio that something was wrong. Since there was no mayday messages from the pilot it leads to the possibility that the pilot was involved.
It seems highly unlikely that the pilot would have the technical programming abilities to write a sophisticated set of code that would be involved in a cyber-hijacking. This means that a cyber-hijacking would have to be a team effort. The pilot for his abilities with flying the aircraft, knowledge of the air corridors, and unrestricted access to the cock-pit for manual maneuvers such as turning off the transponder. If the effects of a cyber attack on the plane was disabling certain programs, beacons, etc that the pilot would not normally be able to alter and was carried out via a cell phone there would be no need for additional team members to physically board the plane. The pilot could carry the phone, and activate the code insertion himself, or another member could physically board the plane who may or may not be the person who wrote the code. Regardless of the number of members on board the plane a cyber-hijacking of the plane would require a minimum of two members, the pilot and the code-writer.
It is highly unlikely that the typical image of a "terrorist" that the Western media portrays, i.e. a turban wearing, camel riding, middle-Eastern man in a cave, would either have the knowledge of how a Boeing-777 computer works in order to program code that was effective, or would be in the market for someone to write such code without gaining international attention. On the other hand the United States or Israel could easily gain the knowledge of exactly how the systems work as well as have numerous people already on the payroll with the ability to write such codes.
If a cyber-hijacking occurred in connection with missing Malaysian flight #370 it was not a lone wolf, a rogue pilot, or an Al-Cia-da terrorist. It would have been a highly sophisticated operation that would require the vast resources of a state to carry out. However the Western media will have you believe the exact opposite.
Read more...
Wednesday, July 24, 2013
Is Your Red My Blue? Google's Gatekeeping Abilities.
The title of this article stems from an interesting question I used to find it entertaining to ask people, and engage in the thought conversation that follows.
How do you know that what you see as blue, I also see as blue?
When we are children we learn the colors, and learn to associate them objects. Objects the look the same color as the object originally associated with a color in turn are also associated with that color. We learn that the sky is blue. The ocean looks similar to the sky, therefor it is also blue. However, if one of us actually saw the sky as red, we would see the ocean looking like the sky, however we are told that the sky is "blue". So although we are seeing two totally different colors we will not know this because since our information is coming from a unified source, be it our parents or the schooling system, when asked "what color is the sky" we will both respond blue.
What does this have to do with Google? Quite literally a gatekeeper is someone who holds the keys, to access something. In the current day a gatekeeper is someone usually associated with having the illusion of providing information will covertly keeping information from people, or giving them false or misleading information.
It is currently believed that most people in the U.S. have access to an open internet. There are relatively few restrictions to what you can access on the "internet" as it is known within the basic domain name structures of www, and ignoring the deeper "darknets" and parts of the internet people either don't know exist or don't have the technical knowledge to know how they operate. If you want to look up something, you have the free will to do so. From pornography to cooking tips, if you want it, you can find it.
Some areas of the world do not have that apparent freedom, however. For example China has large sections of the internet blocked off. When attempting to access a website they will never get the return signal, it will be intercepted, and blocked, or their request will never be allowed to be sent. This allows the administrators to determine what a person is allowed to access, or not. Material that is negative to the ruling administration in China is often censored. Likewise many companies block access to gaming websites to keep their employees productivity higher, and schools block access to pornography to prevent students from accessing that type of adult content.
Read more...
How do you know that what you see as blue, I also see as blue?
When we are children we learn the colors, and learn to associate them objects. Objects the look the same color as the object originally associated with a color in turn are also associated with that color. We learn that the sky is blue. The ocean looks similar to the sky, therefor it is also blue. However, if one of us actually saw the sky as red, we would see the ocean looking like the sky, however we are told that the sky is "blue". So although we are seeing two totally different colors we will not know this because since our information is coming from a unified source, be it our parents or the schooling system, when asked "what color is the sky" we will both respond blue.
What does this have to do with Google? Quite literally a gatekeeper is someone who holds the keys, to access something. In the current day a gatekeeper is someone usually associated with having the illusion of providing information will covertly keeping information from people, or giving them false or misleading information.
It is currently believed that most people in the U.S. have access to an open internet. There are relatively few restrictions to what you can access on the "internet" as it is known within the basic domain name structures of www, and ignoring the deeper "darknets" and parts of the internet people either don't know exist or don't have the technical knowledge to know how they operate. If you want to look up something, you have the free will to do so. From pornography to cooking tips, if you want it, you can find it.
Some areas of the world do not have that apparent freedom, however. For example China has large sections of the internet blocked off. When attempting to access a website they will never get the return signal, it will be intercepted, and blocked, or their request will never be allowed to be sent. This allows the administrators to determine what a person is allowed to access, or not. Material that is negative to the ruling administration in China is often censored. Likewise many companies block access to gaming websites to keep their employees productivity higher, and schools block access to pornography to prevent students from accessing that type of adult content.
Read more...
Labels:
cyber security,
Google,
Prison Internet,
Psychology,
Social Media,
Technology
Friday, June 28, 2013
Google Reads Your E-Mail Before You Send It (But Everyone Already Knew)
One of the biggest big brother issues that has recently been revealed has been that of the PRISM program. A N.S.A. program that installs hubs into the servers of various companies, and collects EVERYTHING, on EVERYONE without a warrant.
Unfortunately this has been known for quite some time by the people "in the know" sort to speak, however, it has been obvious, but ignored by those who had this information put literally in front of their faces.
Read more...
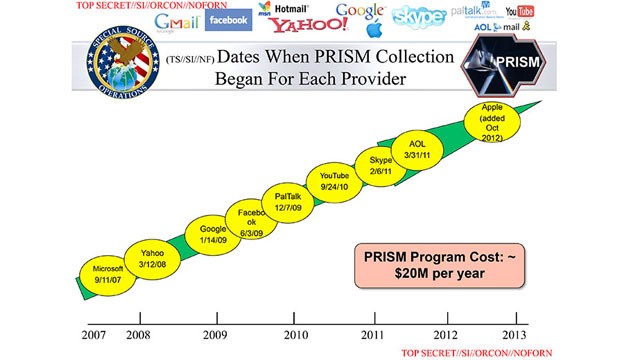 | |||||||
| Leaked Official PRISM Slide - with PRISM targets. |
Unfortunately this has been known for quite some time by the people "in the know" sort to speak, however, it has been obvious, but ignored by those who had this information put literally in front of their faces.
Read more...
Monday, June 18, 2012
Google Purposely Scaring Users with Login-Errors (New Spin on Year-Old Tactics)
Google likes to scare users by displaying red, bold text stating the horrible things that will happen "if" they should lose access to your account.
I reported on this issue last summer, in this article, and the practice is still continuing one year later. The image on the top was taken around 6:00P.M. E.S.T on June 16th, 2012 while attempting to login to my Google (Gmail, and Google Drive) account.
This image appeared after entering the same password 3-4 times, on two different Google login platforms, Gmail and Google Drive. The password was entered manually each time, meticulously as I was thinking I may have been hacked since I knew I was entering the correct password, which on the last attempt worked, and prompted the page screen shot below.
Google has multiple variants of this implementation shown in the image below, also from previous article.
Last year when I originally wrote about this topic it seemed both benign, and an invasion of privacy. Google wanted to gain information, so they attempted to gain phone numbers. Ultimately they want a database of all human knowledge, including all knowledge that exists anywhere about you. They want to know everything.
A year ago I declined to give my phone number, although as many who attempt to fight the good fight we often have to use the tools of the enemy to our advantage. A year after the first report I have an android phone, of which is already synced to my Google account. It didn't matter this time that they wanted it, I entered it, whatever.
The problem was how Google went about it. I believe they crossed a major ethical line. I believe Google is now operating a moderated script of one that was running last summer causing the phone number prompts.
As of now this is speculation, and I have no proof that it exists or that I will be able to find such proof before it disappears. I welcome any, and all to try to support my hypothesis or disprove it. Please pardon any techno-babble below. Below is my hypothesis on the maliciously designed Google script that is operating in the wild across the Google Umbrella Network.
Read more...
I reported on this issue last summer, in this article, and the practice is still continuing one year later. The image on the top was taken around 6:00P.M. E.S.T on June 16th, 2012 while attempting to login to my Google (Gmail, and Google Drive) account.
This image appeared after entering the same password 3-4 times, on two different Google login platforms, Gmail and Google Drive. The password was entered manually each time, meticulously as I was thinking I may have been hacked since I knew I was entering the correct password, which on the last attempt worked, and prompted the page screen shot below.
 |
| Screen shot is of a prompt-screen in between a successful login to a Google service, and that services main page. This would appear between the login page for Gmail, and the user gaining access to then Gmail inbox. No time stamp information is currently available for this image. Image Source |
Google has multiple variants of this implementation shown in the image below, also from previous article.
 |
| Screen Shot Taken: 8/31/11 12:32 AM Screen shot is of a prompt-screen in between a successful login to a Google service, and that services main page. This would appear between the login page for Gmail, and the user gaining access to then Gmail inbox. Image Source |
Last year when I originally wrote about this topic it seemed both benign, and an invasion of privacy. Google wanted to gain information, so they attempted to gain phone numbers. Ultimately they want a database of all human knowledge, including all knowledge that exists anywhere about you. They want to know everything.
A year ago I declined to give my phone number, although as many who attempt to fight the good fight we often have to use the tools of the enemy to our advantage. A year after the first report I have an android phone, of which is already synced to my Google account. It didn't matter this time that they wanted it, I entered it, whatever.
The problem was how Google went about it. I believe they crossed a major ethical line. I believe Google is now operating a moderated script of one that was running last summer causing the phone number prompts.
As of now this is speculation, and I have no proof that it exists or that I will be able to find such proof before it disappears. I welcome any, and all to try to support my hypothesis or disprove it. Please pardon any techno-babble below. Below is my hypothesis on the maliciously designed Google script that is operating in the wild across the Google Umbrella Network.
Read more...
Labels:
cyber security,
Google,
Tracking
Thursday, April 5, 2012
Augmented Reality - Google "Glass"
Augmented reality is not a new concept, however we have just come to a point where today's technology are able to implement the features in a way that will make it work for the layman.
One especially creepy aspect is in the last scene, where the character we are following is able to share his view of the sunset with another person. This could be modified to allow anyone to see exactly what another person is viewing, and doing. Regardless of if the police want to catch crime by seeing drug deals sell drugs, or they simply want to see images of naked women, a tactic borrowed from the T.S.A.
This article was a quick introduction in Google's Glass program, and some of the implications it imposes. Over the next few days, and weeks, more in depth articles will be written showing just how slippery a slope the Glass project can be.
Read more...
This will be the first of several segments on Google "Glass", and the problems that are inherently built into the devices, and programs. Problems that could be accidental, or intentionally placed there as a back door into our lives.
*As of April 5th, 2012 this video has begun to go viral, being picked up by several news agencies.
One especially creepy aspect is in the last scene, where the character we are following is able to share his view of the sunset with another person. This could be modified to allow anyone to see exactly what another person is viewing, and doing. Regardless of if the police want to catch crime by seeing drug deals sell drugs, or they simply want to see images of naked women, a tactic borrowed from the T.S.A.
Technology is growing at a staggering rate, and the amount of people who have significant computing skills is growing every day, thanks in part to the availability of devices such as iPhones, and iPads. Combined this with the power of the masses, such as the hacktivist group Anonymous, and you could end up with major security breaches.
Cell phone calls, and records have already been hacked. The Murdoch example is just one of many, Another recent example is the hacked emails from Stratfor. Each of these security breaches is significant, however imagine how much more severe it would be if someone could see what you are seeing, exactly where you are, etc.
Cell phone calls, and records have already been hacked. The Murdoch example is just one of many, Another recent example is the hacked emails from Stratfor. Each of these security breaches is significant, however imagine how much more severe it would be if someone could see what you are seeing, exactly where you are, etc.
A cloned device that only shows what the original device is "seeing" or doing would allow people to know exactly where a person is, who they are with, when they will be home, and a host of other issues.
This article was a quick introduction in Google's Glass program, and some of the implications it imposes. Over the next few days, and weeks, more in depth articles will be written showing just how slippery a slope the Glass project can be.
Read more...
Subscribe to:
Posts (Atom)
Disclaimer
A new disclaimer is currently being written, and will be posted in this space when available.
Xieon Politics
.
Categories
2012 Election
(4)
9/11
(6)
Abortion
(1)
ACLU
(1)
ACORN
(3)
Afghanistan
(3)
Al Gore
(3)
Al-CIA-da
(6)
Alex Jones
(2)
Alinsky
(2)
Anita Dunn
(1)
Anonymous
(1)
Apple
(1)
Axelrod
(1)
backdoor apps and services
(2)
Bailout
(1)
Bank of America
(1)
Banking
(1)
Batman Shooting
(2)
Bible
(1)
bilderberg
(4)
Bill of Rights
(1)
Bin-Laden
(4)
blog changes
(1)
Border Security
(1)
Boston
(3)
Boston Marathon
(5)
BPA
(1)
Cancer
(4)
cause
(1)
censorship
(5)
chem planes
(1)
chemtrails
(1)
Chicago
(5)
Children
(1)
Christianity
(1)
Christmas
(1)
civil war
(2)
Climate Change
(3)
Clouds
(1)
CNN
(2)
Colorado
(1)
Common Law and Ethics
(1)
Computing
(7)
conspiracy
(1)
Constitution
(3)
Corbett
(1)
Corruption
(2)
Cover Story
(1)
crime
(1)
cyber security
(8)
Czar
(1)
Dick Cheney
(1)
Dinosaur Media
(2)
Disclaimer
(1)
DNA
(1)
DOJ
(1)
DTA
(2)
DUA
(1)
Dzhokhar
(1)
EBT
(2)
economics
(2)
Education
(1)
Egypt
(1)
Elections
(6)
Emmanuel
(1)
EU
(1)
Eugenics
(6)
F.E.M.A
(3)
Facebook
(6)
False Flag
(8)
FDA
(1)
flat earth
(1)
Food Stamps
(2)
foreign officials
(2)
Foreign Policy
(3)
Fort Hood
(1)
FOX
(2)
Fox News
(6)
fragment
(6)
Freedom of Information
(1)
Fringe Media
(3)
Ft. Hood
(1)
GE
(1)
Global Warming
(3)
Globalism
(1)
Globalist
(1)
Google
(8)
google bomb
(5)
Government Document
(1)
Green
(1)
Green Police
(2)
Guerrilla Info-Warfare
(2)
Gun Confiscation. vode
(1)
gun control
(2)
Gun Rights
(1)
Guns
(1)
H1N1
(1)
Healthcare
(10)
Holmes
(1)
Homeland Security
(1)
I.R.S.
(2)
Illuminati
(1)
Immigration
(3)
Indoctrination
(4)
information collection
(5)
Infowars
(1)
Interview
(2)
Janet Reno
(1)
Japan
(3)
JonBenet
(1)
Judge Watch
(1)
Liberals
(1)
Libya
(2)
Local
(2)
Malaysian Airlines Flight 370
(6)
marbury v madison
(1)
Massachusetts
(10)
McPhee
(4)
Media Bias
(9)
Medical
(1)
Memorial Day
(1)
MH-17
(1)
MH-370
(1)
Michele McPhee
(2)
Microsoft
(1)
Military
(2)
Millitary
(2)
moon
(1)
Name Change
(1)
Nancy Pelosi
(1)
New Blog
(2)
New World Order
(3)
NORAD
(1)
November 2010
(5)
NSA
(2)
Obama
(22)
Occult
(1)
Olympics
(2)
Open Letter
(1)
Oregon
(1)
Organized Religion
(1)
Pakistan
(4)
Palin
(1)
Parenting
(1)
past presidents
(1)
Police
(1)
police state
(15)
Political Correctness
(2)
posse comitatus
(1)
PRISM
(2)
Prison Internet
(20)
propaganda
(2)
Psychology
(1)
racism
(2)
Rant
(1)
religion
(3)
Richard Quest
(1)
Rick Perry
(5)
Ron Paul
(6)
Rush Limbaugh
(1)
Russia
(1)
satire
(6)
Screenshot
(1)
scrubber
(2)
Scrubbing
(1)
Second Amendment
(3)
secrecy
(3)
See Something Say Something
(1)
Sibel Edmonds
(1)
sky
(1)
sky pictures
(1)
Smartphone
(1)
SNAP
(1)
Snowden
(1)
Social Media
(1)
States Rights
(1)
Swine Flu
(1)
Symbolism
(1)
Syria
(3)
t
(1)
Tamerlan Tsarnaev
(1)
Taxes
(1)
Teaparty
(1)
Technology
(4)
Terrorism
(9)
Time Capsule
(1)
Time Machine
(1)
Tracking
(10)
Tripathi
(1)
TSA
(2)
Twitter
(1)
Unemployment
(1)
United Nations
(2)
Vaccines
(1)
Video
(34)
Wal-Mart
(1)
War
(10)
Watertown
(1)
we are change
(2)
weather
(2)
Webpage Screenshot
(2)
Webster Tarpley
(1)
Welfare
(1)
White House
(1)
world news
(3)
WRKO
(2)
WTKK
(1)
WW3
(3)
Yahoo
(1)
Yemen
(1)

